Enhancing Network Security with AI: A DFIR Perspective

Image from Pixabay
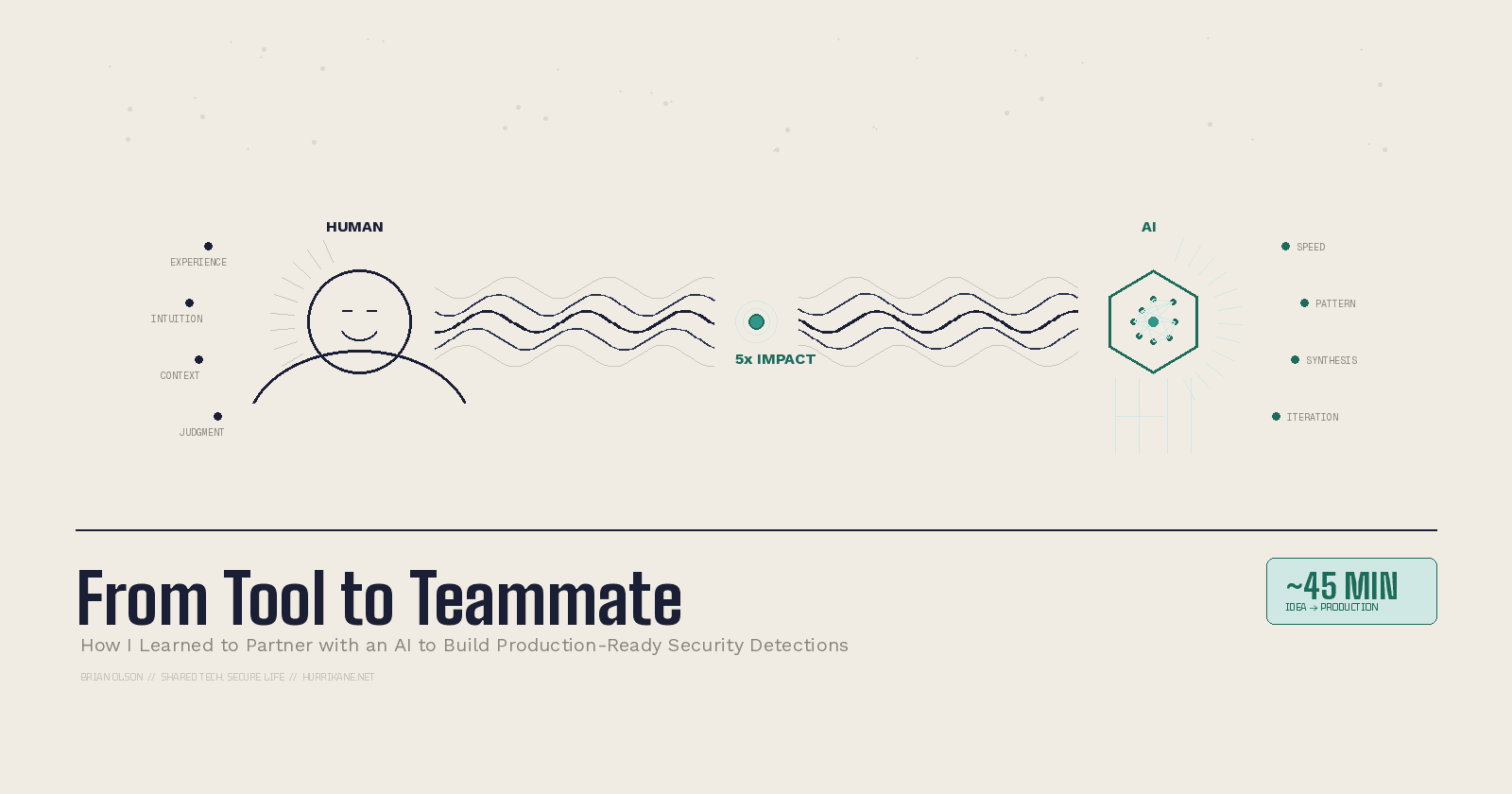
The cybersecurity landscape has entered an era of unprecedented complexity. Cyberattacks unfold at machine speed, with adversaries leveraging automation and AI to bypass traditional defenses. For Digital Forensics and Incident Response (DFIR) professionals, this escalation demands tools that match modern threats’ scale and sophistication. Enter artificial intelligence — a transformative force reshaping network security by augmenting human analysts with capabilities that were once the realm of science fiction. From detecting zero-day exploits to reconstructing attack timelines, AI is revolutionizing how we defend digital ecosystems.
AI-Driven Threat Detection: From Reactive to Proactive Defense
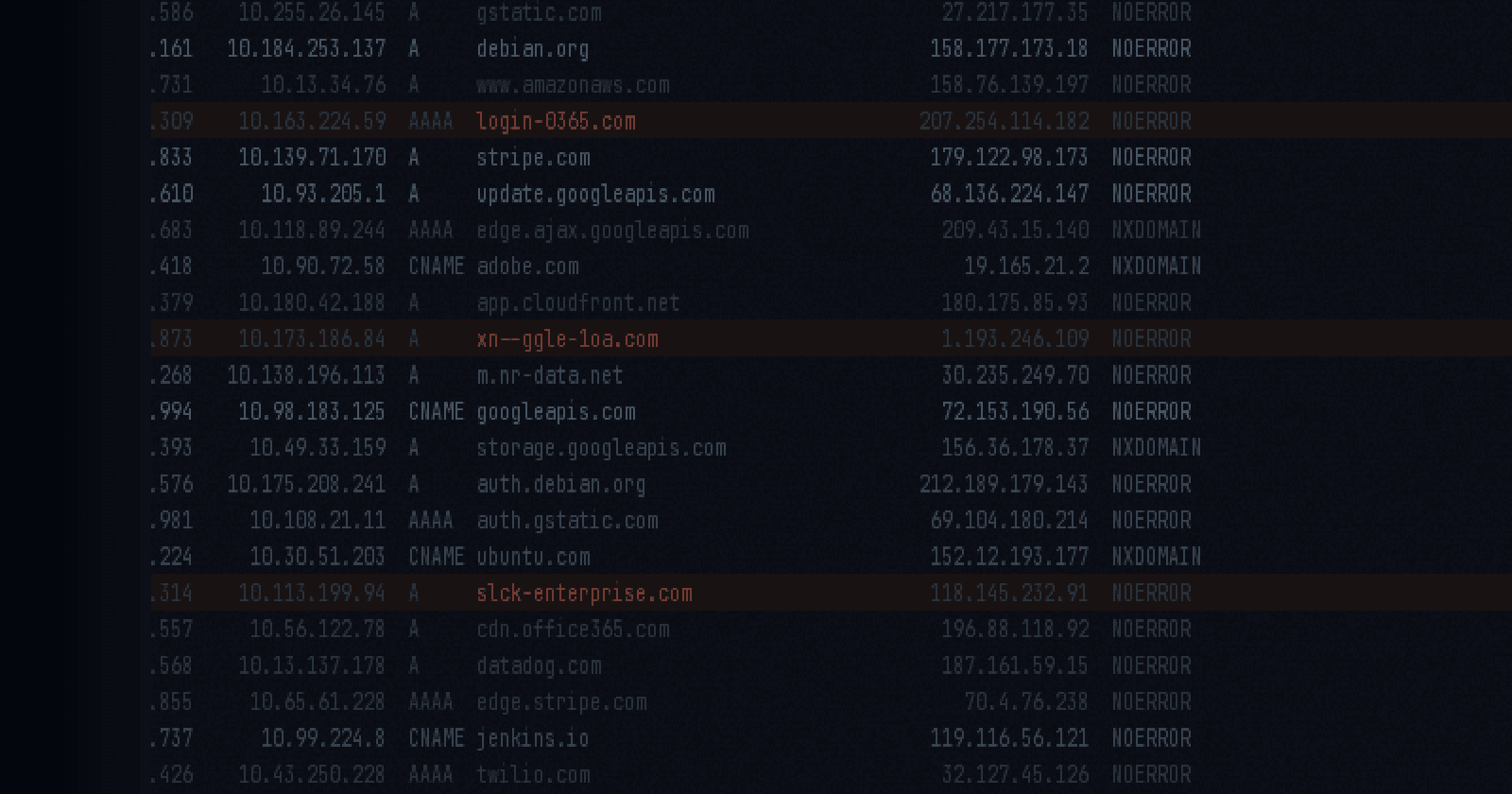
Traditional signature-based detection methods struggle to keep pace with evolving threats like polymorphic malware and advanced persistent threats (APTs). AI-powered systems, however, analyze network traffic in real time, identifying anomalies that evade conventional tools. Machine learning models trained on historical attack data can recognize subtle patterns indicative of malicious activity, such as unusual data exfiltration spikes or unauthorized lateral movement. For instance, supervised learning algorithms classify known threats with 99% accuracy, while unsupervised models detect novel attack vectors by flagging deviations from baseline behavior.
Behavioral anomaly detection is particularly effective for combating insider threats. By establishing “normal” user activity profiles—such as login times, data access patterns, and device usage—AI systems can alert DFIR teams to deviations like a finance employee accessing sensitive R&D files at 3 AM. Case in point: Intezer’s Autonomous SOC platform reduced false positives by 70% while identifying 40% more threats in a 2024 enterprise deployment.
AI in Incident Response: Accelerating Time-to-Resolution
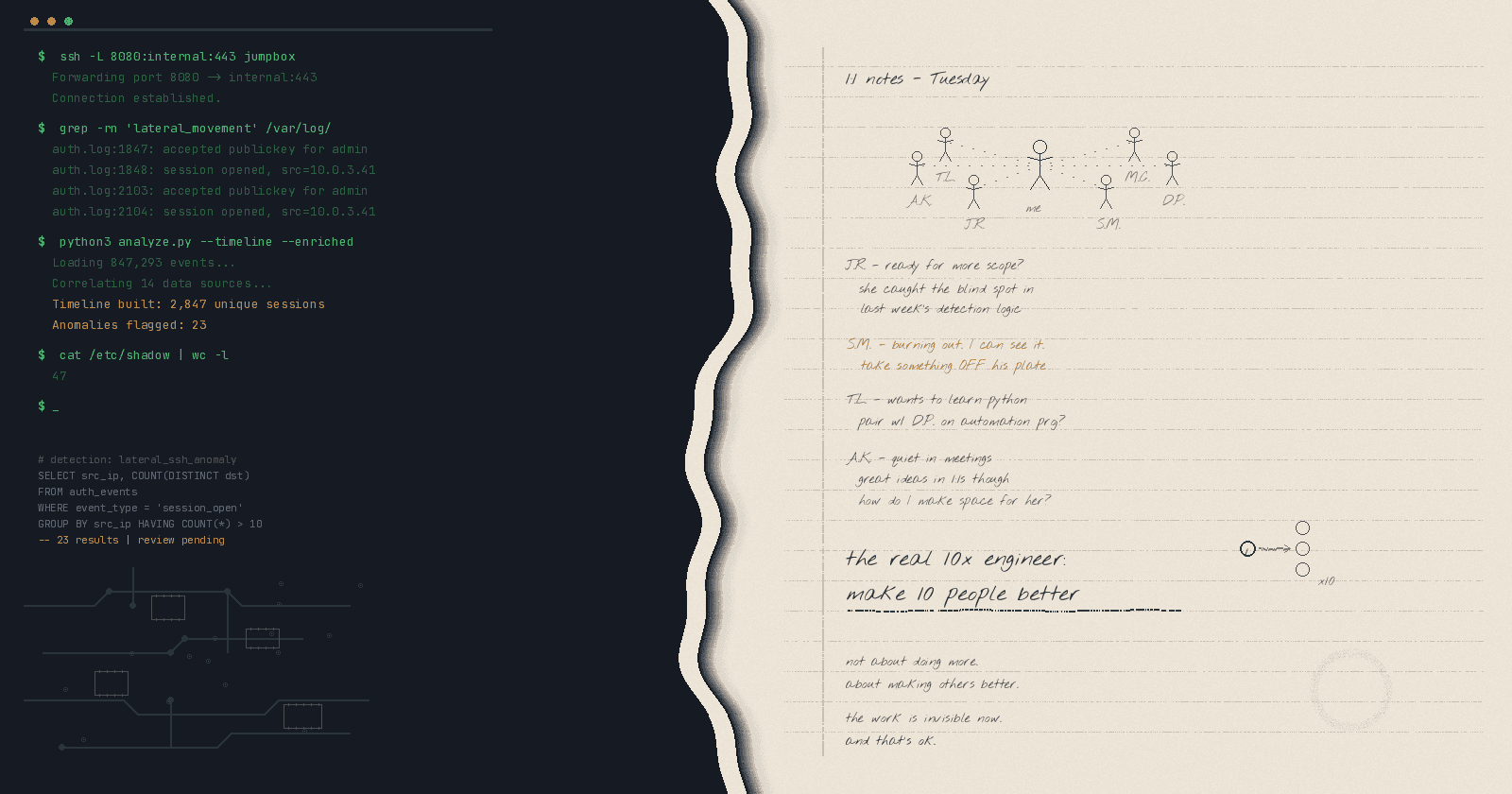
When a breach occurs, every second counts. AI streamlines incident response by automating time-consuming tasks like log analysis and alert triage. Natural language processing (NLP) tools parse thousands of alerts daily, prioritizing critical incidents (e.g., ransomware activity) over low-risk events (e.g., failed login attempts). This allows DFIR teams to focus on high-impact investigations rather than drowning in noise.
Forensic analysis also benefits from AI’s pattern recognition prowess. During a recent supply chain attack, an AI tool reconstructed the attack timeline in 12 minutes — a task that would have taken a human analyst days. By cross-referencing malware hashes with global threat databases like VirusTotal, AI identified the attacker’s infrastructure and linked it to a known state-sponsored group. Such speed is critical for containing breaches before they escalate.
AI-Enhanced DFIR Capabilities: Beyond Human Limits
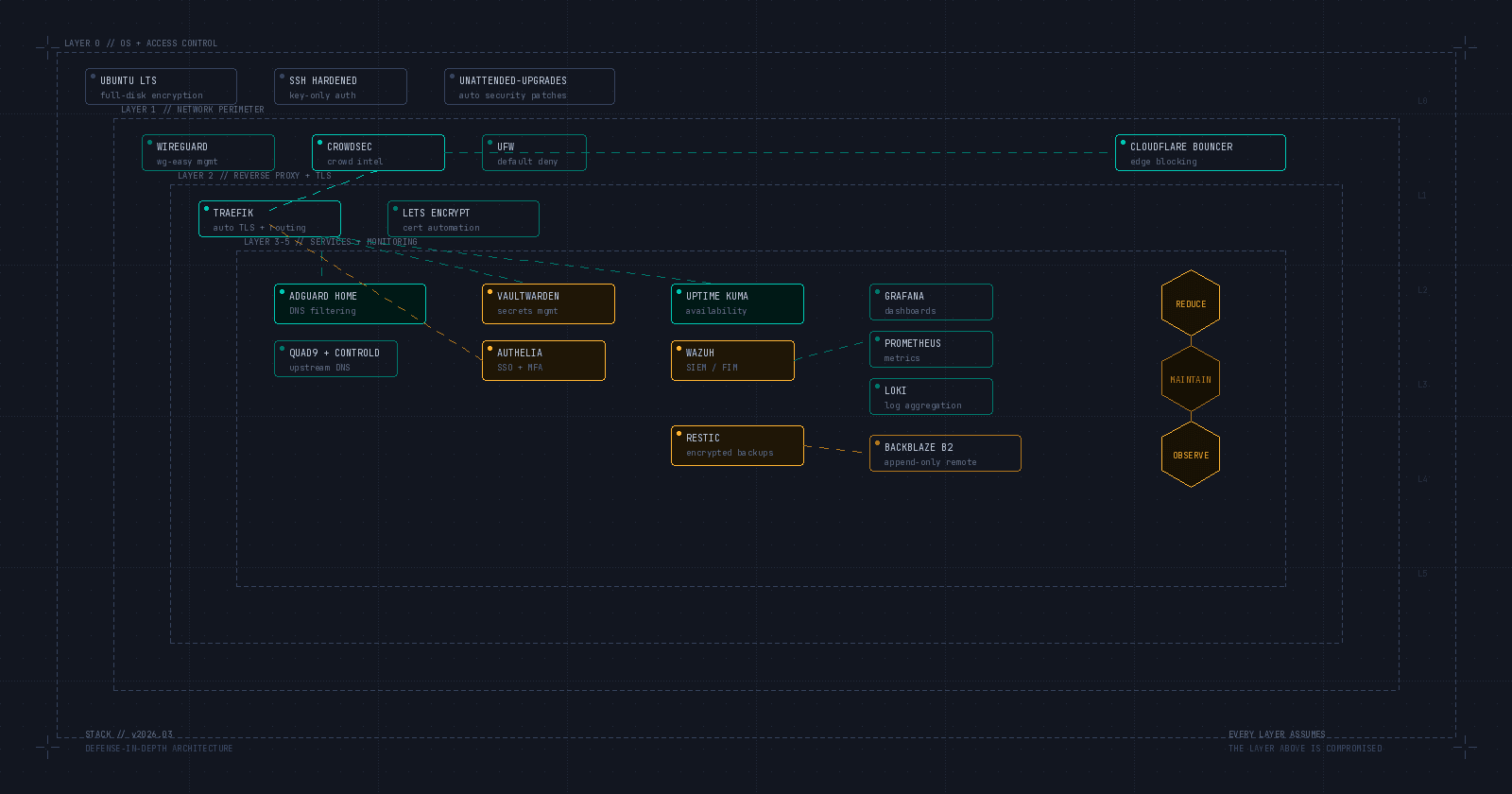
Modern networks generate petabytes of logs daily, creating a haystack where critical evidence often hides. AI excels at finding needles in this haystack. For example:
- Log Analysis: Transformer-based models (like GPT-4) summarize logs into actionable insights, highlighting suspicious IP addresses or unusual protocol usage.
- Evidence Preservation: Automated systems create forensic snapshots of compromised devices, ensuring chain-of-custody compliance while eliminating human error.
- Predictive Analytics: By correlating current threats with historical data, AI forecasts attack vectors, enabling preemptive hardening of vulnerable systems.
In one case, a financial institution used AI to analyze 18 months of network traffic, uncovering a dormant APT that had evaded detection by traditional IDS solutions. The AI flagged irregular DNS queries masked as routine cloud backups, leading to the discovery of a sophisticated data exfiltration scheme.
Challenges to Consider
While AI offers immense potential, it is not a silver bullet. Adversarial machine learning — where attackers poison training data or manipulate models — poses significant risks. For instance, researchers recently demonstrated how subtly altered network packets could trick AI systems into classifying ransomware traffic as benign. DFIR teams must rigorously validate AI outputs and maintain human oversight.
The Future of AI in DFIR
Looking ahead, three trends will dominate:
- AI-Quantum Hybrids: Quantum computing will turbocharge AI’s ability to decrypt intercepted communications and simulate attack scenarios.
- Privacy-Preserving AI: Federated learning models will analyze sensitive data without centralized storage, reducing breach risks.
- Autonomous Response: Self-healing networks will automatically isolate compromised nodes and deploy patches, minimizing downtime.
Conclusion
I truly believe that AI won’t replace DFIR professionals — it’s empowering and supercharging them. By automating mundane tasks and surfacing hidden threats, AI allows analysts to focus on strategic decision-making and creative problem-solving. However, success hinges on balancing innovation with vigilance. As cyber adversaries increasingly weaponize AI, defenders must stay ahead by fostering collaboration between human expertise and machine intelligence. For DFIR teams, the message is clear: adapt or become obsolete.