Why Self-Hosting Matters More Than Ever in 2026
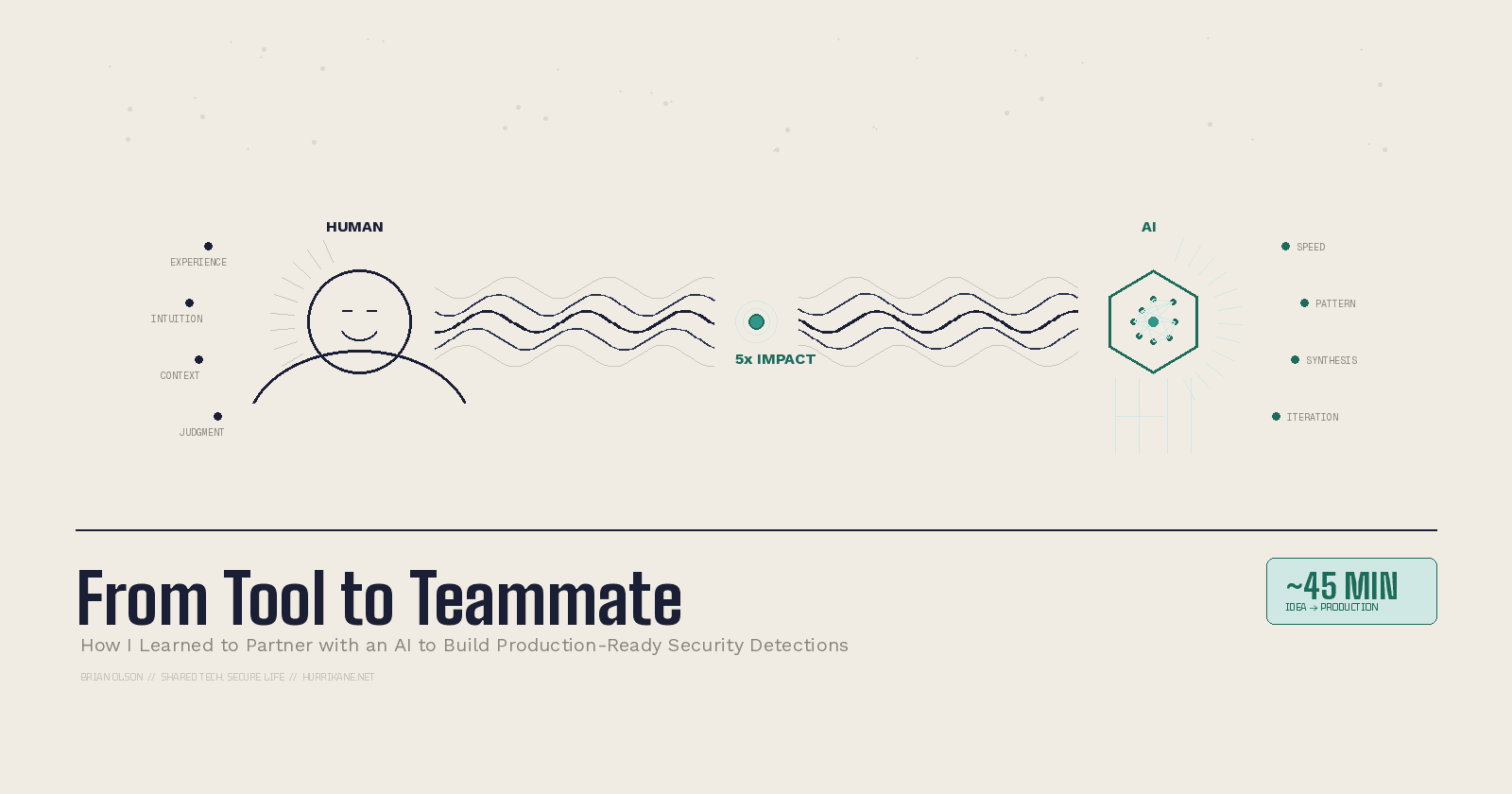
I’m Brian Olson, a cybersecurity professional with deep experience in DFIR and network forensics—currently working in Big Tech. My mission? To share hard-won lessons not just with fellow experts, but with anyone learning and growing in security—especially those in smaller companies without the resources or teams a massive enterprise has. I started blogging to break down real-world strategies, honest tool reviews, and battle-tested workflows in plain language. Whether you’re an underdog SOC analyst or a curious IT pro tackling security for the first time, my goal is to make the practical side of cybersecurity a little less overwhelming—and a lot more actionable. Expect guides that cut through the noise, resources that are actually useful at the keyboard, and stories that prove you don’t need a giant budget to make a real impact. You’ll also find my takes on personal finance, real estate, and anything that helps us level up—in and out of work. Let’s connect. We’re all in this together!
As someone who's spent nearly two decades in cybersecurity—responding to breaches, hunting threats across enterprise networks, and teaching DFIR at SANS—I've watched the industry oscillate between "move everything to the cloud" and "wait, maybe we shouldn't have done that." In 2026, the pendulum is swinging hard toward a conclusion I've been arriving at personally: if you care about your data, your privacy, and your long-term autonomy, it's time to seriously consider self-hosting.
And no, I'm not talking about spinning up a janky Raspberry Pi in your closet (though you can). I'm talking about a fundamental shift in how security-minded professionals and small businesses should think about where their digital lives actually live.
The SaaS Trust Problem
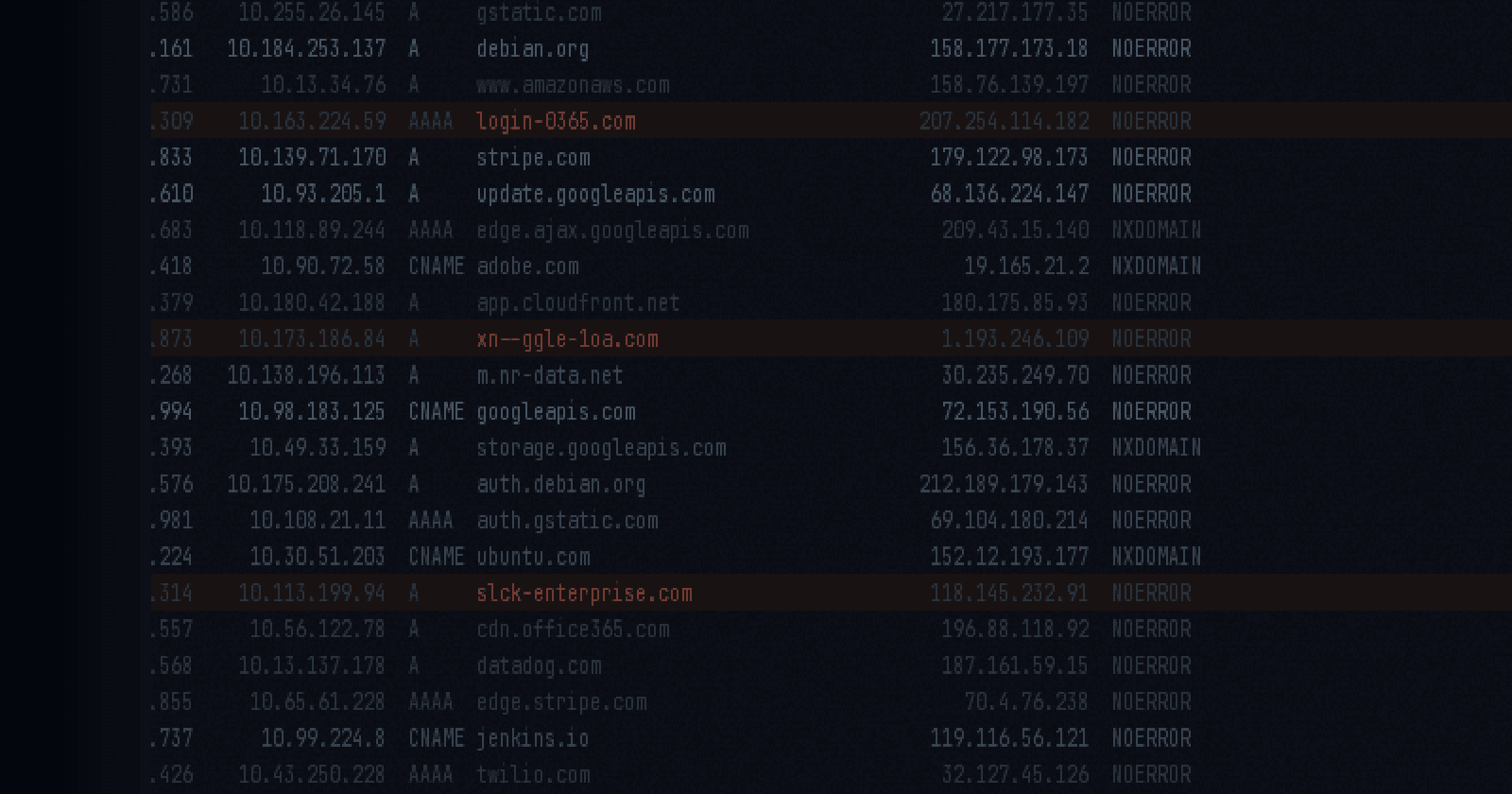
Let me put my DFIR hat on for a second. In 2025, SaaS breaches didn't just increase—they became systematic. The Salesloft-Drift campaign hit over 700 organizations by compromising OAuth tokens. Gainsight followed the same playbook, taking down another 200+ Salesforce instances. ShinyHunters didn't need zero-days. They just exploited trusted integrations—the very connections organizations set up and forgot about.
The average mid-sized company now runs over 200 SaaS applications, and the average cost of a breach sits at $4.4 million. But here's the thing that keeps me up at night: 83% of companies reported experiencing a cloud data breach in 2025, and attackers can move from initial compromise to data exfiltration in as little as nine minutes. Nine. Minutes.
Every SaaS app you onboard is another node in your attack surface. Every OAuth token is a potential pivot point. Every "Connect to Google" button is a trust decision you probably didn't fully evaluate. As someone who's been on the response side of these incidents, the pattern is unmistakable: the more you distribute your data across third-party platforms, the harder containment becomes and the longer breaches go undetected.
The Regulatory Reckoning
The regulatory landscape has caught up to what security practitioners have been saying for years. The EU AI Act becomes fully enforceable in August 2026. GDPR fines topped €6.7 billion since inception, with enforcement accelerating year over year. The U.S. Department of Justice now restricts sharing sensitive American data with certain countries. Eighteen states have active privacy laws. India, China, and Saudi Arabia are all tightening data localization requirements.
The direction is unmistakable: governments worldwide are asserting that data should stay under the jurisdiction where it's created and processed. The era of "just throw it in AWS and hope for the best" is ending—not because the technology failed, but because the legal and geopolitical reality caught up.
For small businesses and solo operators, this creates an interesting paradox. You're subject to increasingly strict data handling requirements, but your SaaS providers may be storing your customer data across jurisdictions you can't even identify. Self-hosting doesn't eliminate compliance complexity, but it does give you a clear answer to "where is my data?"—it's wherever you put it.
The Cost Equation Has Flipped
I've written before about cutting digital fat and trimming subscriptions. Here's what most people don't calculate: the cumulative cost of SaaS sprawl over time versus the one-time investment in self-hosted infrastructure.
A basic stack of cloud productivity tools—email, storage, project management, password manager, VPN, notes, calendar—can easily run \(50-100/month per person. Over five years, that's \)3,000-6,000, and you own nothing. Your data lives on someone else's servers, governed by their terms of service, which they can change whenever they want.
Compare that to a VPS from Hetzner, DigitalOcean, or even a mini PC sitting in your closet. For \(10-20/month (or a one-time \)200-400 hardware investment), you can run Nextcloud for files and calendar, Vaultwarden for passwords, a Tailscale mesh for private networking, and a growing ecosystem of containerized apps that replace nearly every SaaS tool most individuals and small teams rely on.
The math doesn't lie. But the real savings aren't just financial—they're in reduced risk. Fewer accounts means fewer credentials to manage, fewer OAuth grants to audit, fewer vendors who might get breached with your data inside.
The Tooling Is Finally Ready
I'll be honest—three or four years ago, I would have hesitated to recommend self-hosting to anyone who wasn't already comfortable with Linux and Docker. The operational burden was real. Updates were painful. Backup strategies were DIY at best.
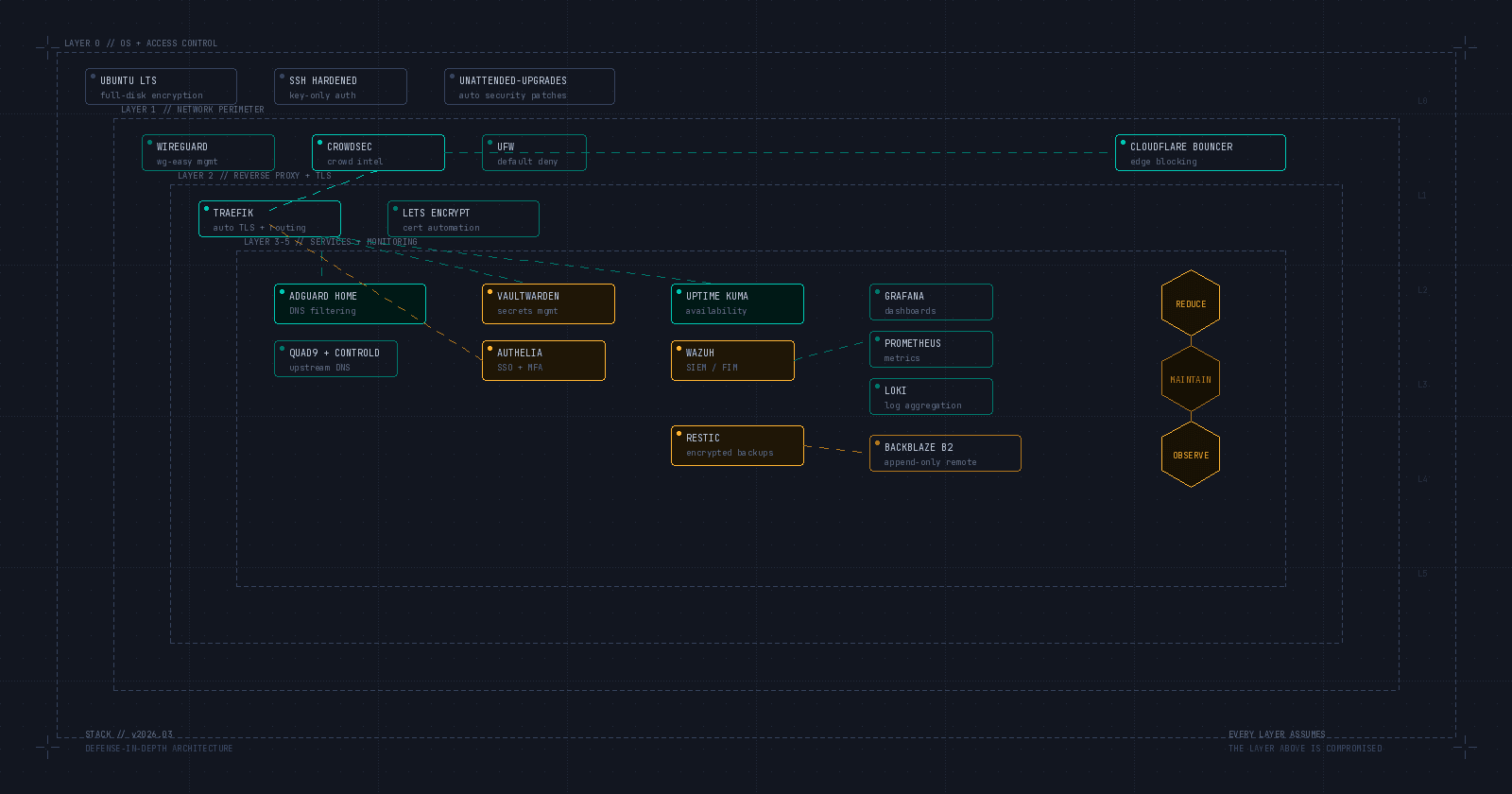
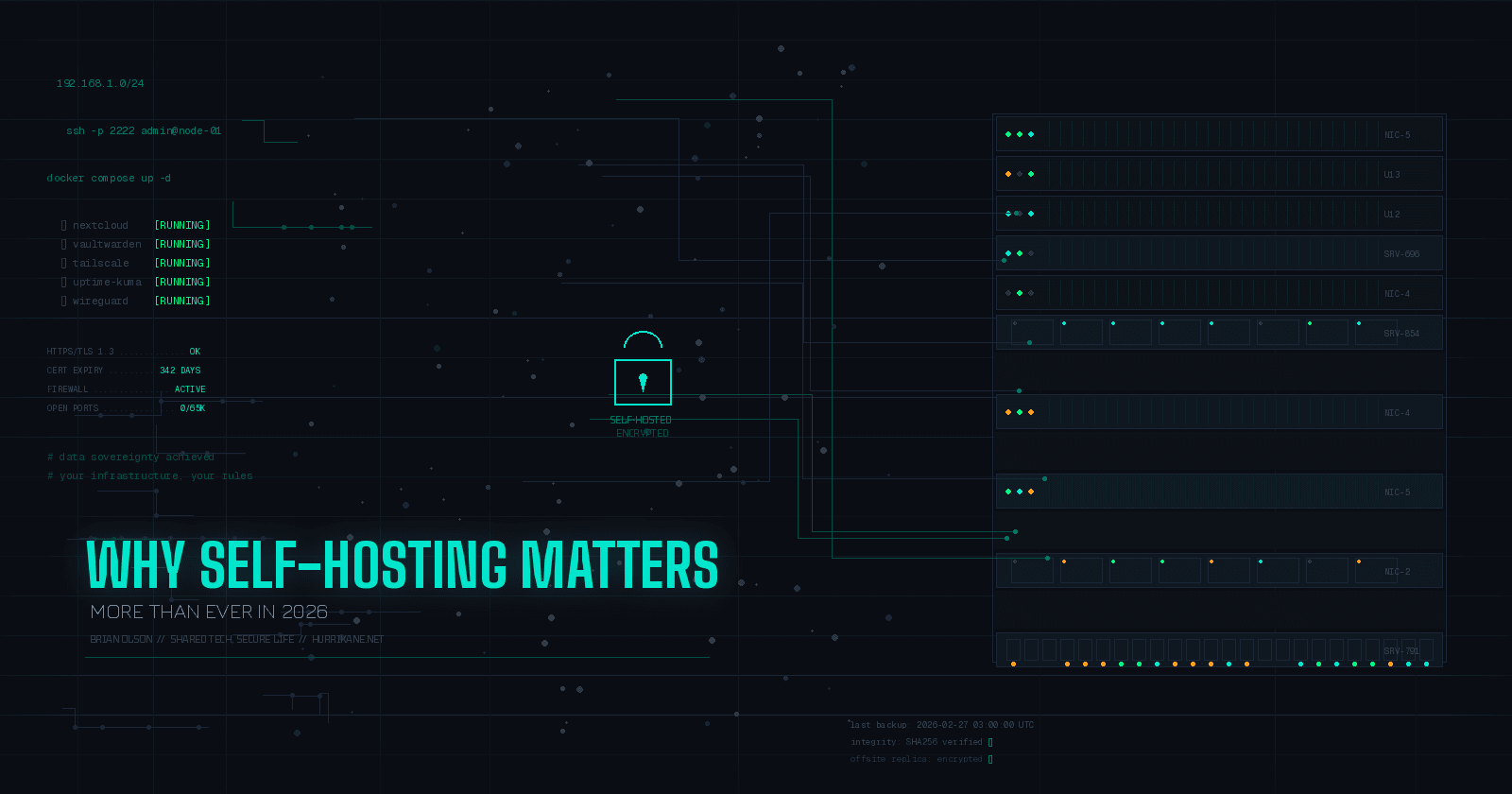
That's changed. Docker Compose has made deploying complex application stacks almost trivially simple. Projects like Nextcloud, Immich, Paperless-ngx, and Vaultwarden have matured into genuinely polished products with active communities and regular security updates. Tailscale and WireGuard have solved the networking problem—you can securely access your self-hosted services from anywhere without exposing a single port to the internet.
For the security-conscious, this is particularly compelling. Instead of trusting a VPN provider (and I've written about the hidden dangers of commercial VPNs), you can run your own mesh network where traffic never touches a third party's infrastructure. Your DNS queries can stay local. Your files never leave hardware you control.
The barrier to entry hasn't just lowered—it's practically on the ground for anyone with basic technical literacy.
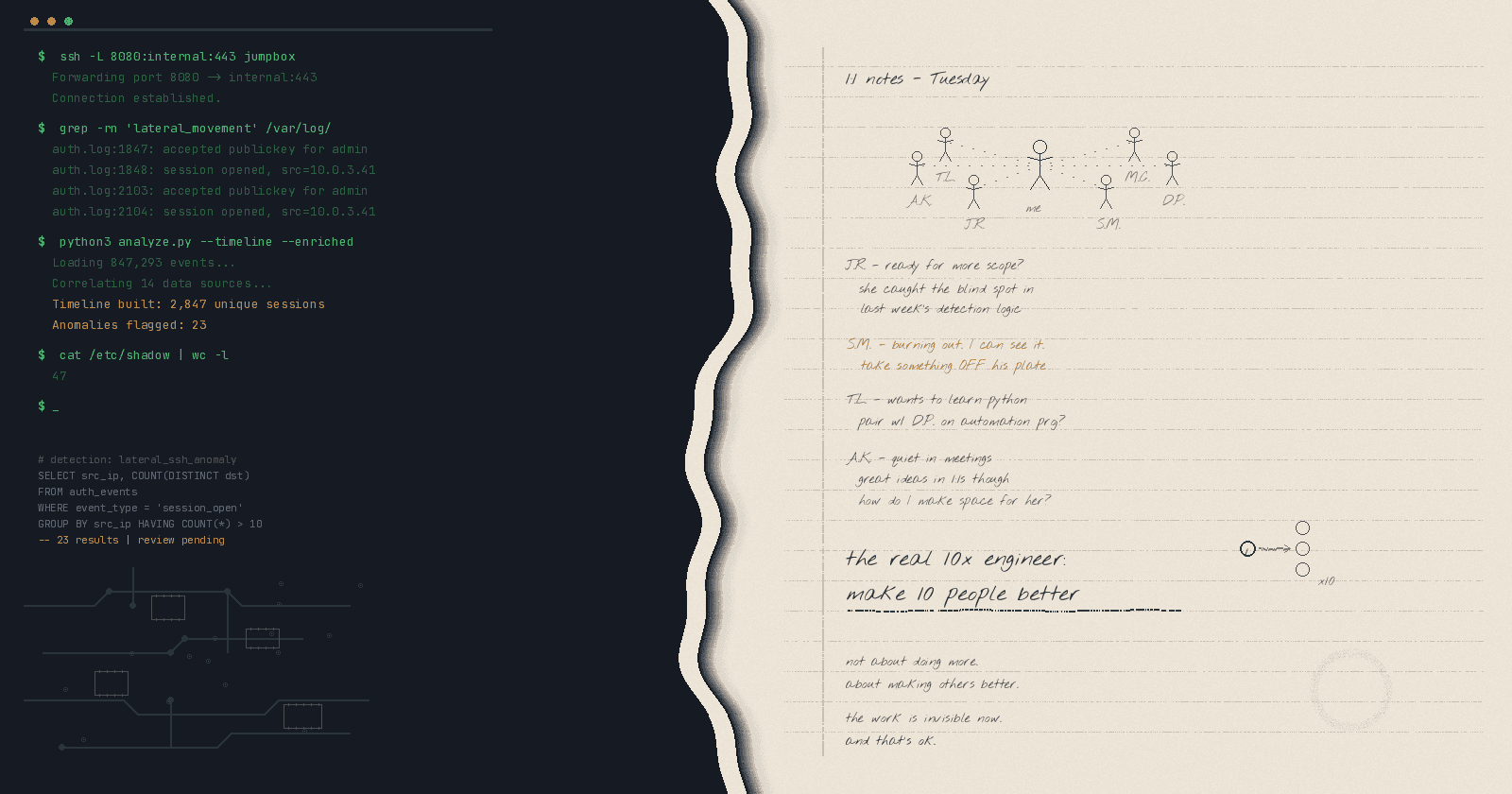
A DFIR Professional's Perspective
Here's what my day job has taught me that most self-hosting advocates don't talk about: operational security doesn't stop at deployment.
Self-hosting means you are the SOC. You need to think about:
Patch management: Are you updating your containers and host OS regularly? Unpatched self-hosted services are worse than SaaS because you don't have a vendor's security team watching your back.
Backup and recovery: The 3-2-1 rule still applies. Three copies, two different media, one offsite. If your self-hosted Nextcloud dies and your only backup is on the same disk, you've accomplished nothing.
Monitoring: At minimum, you should know when services go down, when storage fills up, and when something unexpected happens. Uptime Kuma is free and takes five minutes to deploy.
Access control: Just because it's your server doesn't mean you should run everything as root with default credentials. Treat your self-hosted stack with the same rigor you'd apply to a production environment.
This isn't meant to scare you off. It's meant to set expectations. Self-hosting gives you control, but control comes with responsibility. As someone who responds to incidents for a living, I'd rather see people self-host well than self-host carelessly.
Where to Start
If you're new to self-hosting, don't try to replace everything at once. Start with one service that gives you meaningful privacy gains and build from there:
Password manager (Vaultwarden): This is the highest-impact, lowest-effort starting point. Your credentials are the keys to your entire digital life. Get them off someone else's cloud.
DNS filtering (ControlD, Pi-hole, or AdGuard Home): I've already written about my ControlD setup. This one improves both privacy and security immediately.
Private networking (Tailscale): Once you have services running, Tailscale lets you access them securely from anywhere—no port forwarding, no exposed attack surface.
File storage (Nextcloud): Replace Google Drive or Dropbox for your sensitive documents. Keep the commercial service for stuff you don't care about.
Monitoring (Uptime Kuma): Because if you're going to self-host, you need to know when something breaks.
Each of these can be deployed in under an hour with Docker Compose, and each one removes a dependency on a third party that may or may not have your best interests at heart.
The Bigger Picture
I think the self-hosting movement is about something larger than technology. It's about rejecting the assumption that convenience must come at the cost of control. It's about recognizing that when a service is free, you are the product—and even when you're paying, the vendor's incentives don't always align with yours.
As a cybersecurity professional, I've seen what happens when organizations lose control of their data. The breaches, the incident response scrambles, the regulatory fallout—none of it is theoretical to me. And increasingly, I'm applying those same lessons to my own digital life.
Self-hosting isn't about going off the grid or becoming a digital hermit. It's about being intentional with where your data lives, who has access to it, and what happens when (not if) something goes wrong.
The tools are mature. The cost equation makes sense. The threat landscape demands it. If you've been on the fence, 2026 is the year to start building your own infrastructure—even if it's just one Docker container at a time.
What's your self-hosting setup? Have you started moving off SaaS, or are you still evaluating? Drop a comment—I'd love to hear what tools you're running and what challenges you've hit. If you're new to this and want to see how I set up specific services, let me know and I'll dig into the details in a future post.