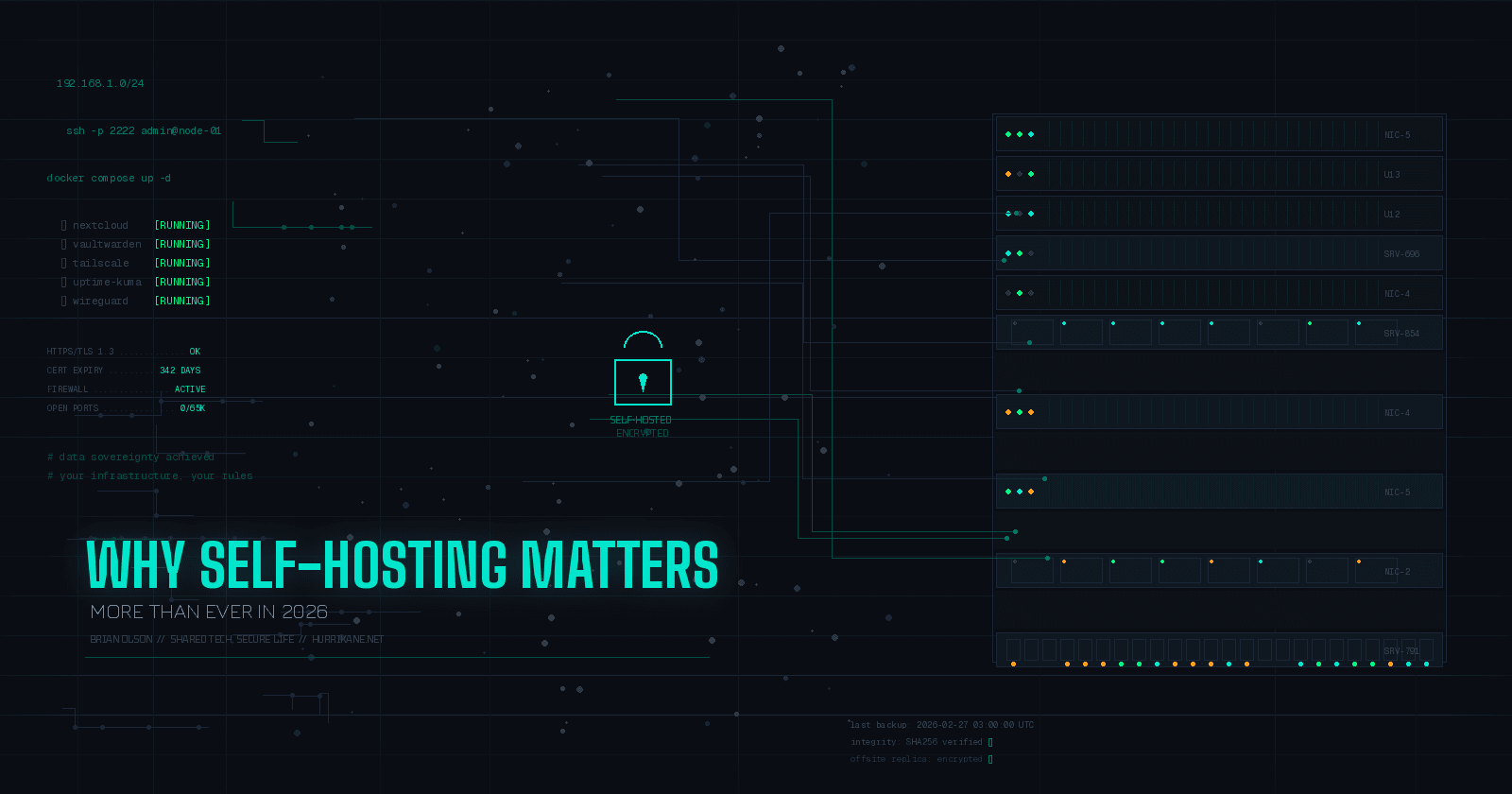
The Hidden Dangers of Commercial VPNs: Why Private Solutions Like Tailscale Are the Future
Image from Pixabay
Virtual Private Networks (VPNs) have become essential tools for privacy-conscious users, promising anonymity and security. However, commercial VPN providers face growing vulnerabilities to government interference, legal pressure, and covert surveillance partnerships. Recent cases like Operation Nova — where law enforcement seized VPN infrastructure across five countries — and revelations about ExpressVPN’s ties to intelligence operatives prove even “secure” services can’t guarantee privacy. This post exposes how governments exploit commercial VPNs and why decentralized alternatives like Tailscale offer fundamentally safer networking.
How Commercial VPNs Work — And Why They’re Vulnerable
The Illusion of Privacy in Centralized Models
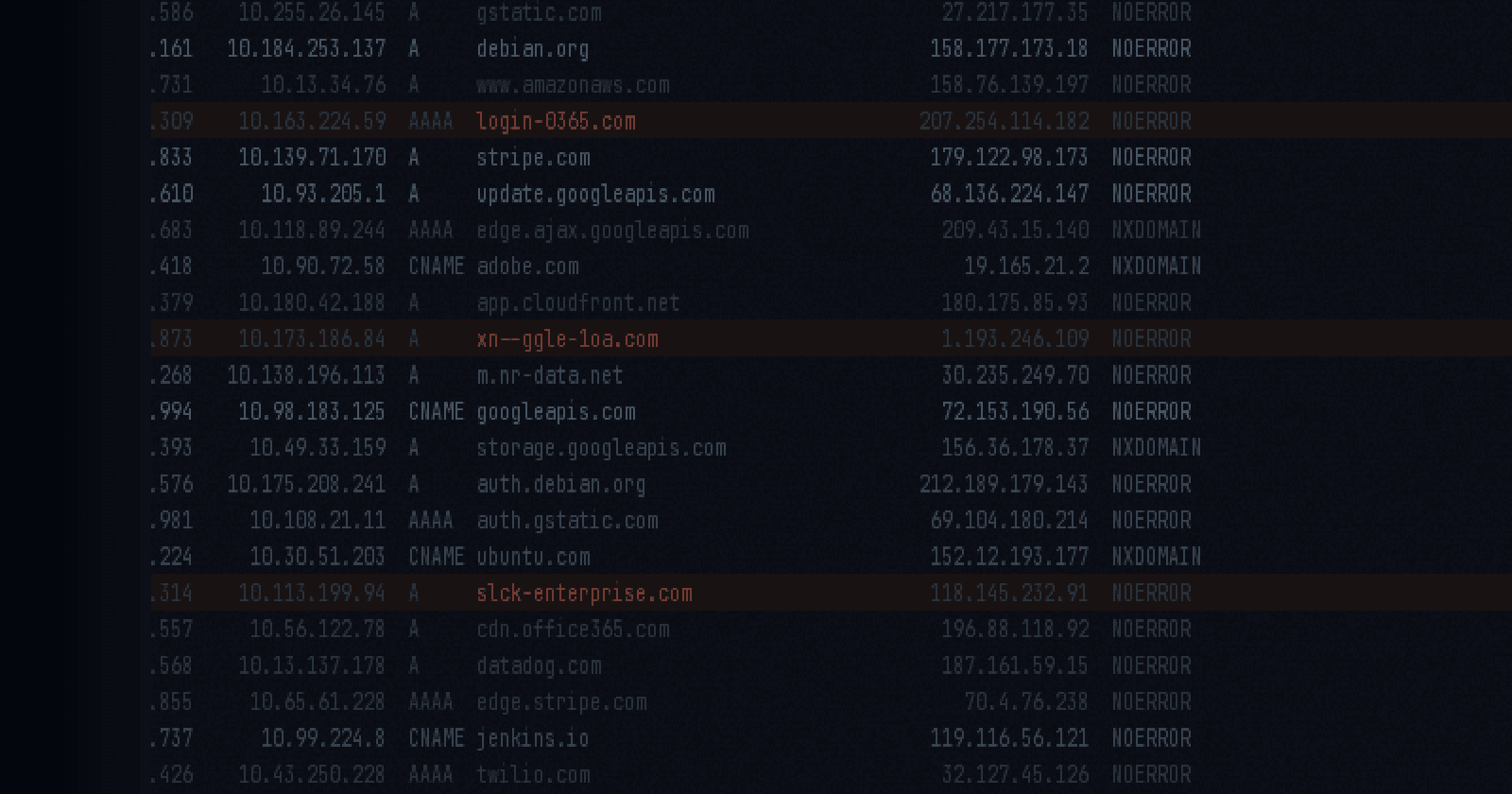
Commercial VPNs route traffic through centralized servers owned by the provider. While this hides activity from your ISP, it grants the VPN company full visibility into:
- Browsing history (even if “no-log” policies exist)
- Device identifiers (IP addresses, geolocation, hardware details)
- Connection timestamps (used to correlate activity in investigations)
These providers often operate in jurisdictions subject to Five Eyes alliance data-sharing agreements, meaning user data requested by one member government can be shared across 14 countries without your knowledge.
Government Takeovers: When “Secure” VPNs Become Surveillance Tools
Example 1: Operation Nova (2020)

In December 2020, German police and the FBI dismantled Safe-Inet, a VPN service allegedly used by ransomware groups. Authorities:
- Seized servers in France, Germany, and the U.S.
- Replaced Safe-Inet’s website with a law enforcement banner
- Accessed logs showing attacks against 250 companies
Why This Matters: Safe-Inet advertised 5-layer encryption and “bulletproof” anonymity but couldn’t resist government seizure. Users’ real IPs were exposed, enabling follow-up arrests.
Example 2: The IPVanish Contradiction
In 2018, IPVanish — a “no-log” provider — handed user data to Homeland Security, revealing a suspect’s Comcast IP address. Despite marketing claims, they retained:
- Connection timestamps
- Bandwidth usage
- Original IP addresses
This case proves U.S. subpoenas override privacy policies, even for providers based in “privacy-friendly” jurisdictions like Panama.
Example 3: ExpressVPN’s Intelligence Ties
ExpressVPN’s Chief Information Officer, Daniel Gericke, was a former U.S. mercenary hacker fined $335K for conducting cyber ops for UAE intelligence. While no direct wrongdoing was proven, this reveals:
- Commercial VPNs’ personnel may have government ties
- Acquisition by Kape Technologies (owner of CyberGhost VPN) created potential conflicts of interest
Legal Frameworks Enabling Government Access
1. Data Retention Laws
Countries like Australia and the UK mandate VPNs store:
- Connection logs (IPs, timestamps) for 2+ years
- Metadata sufficient to identify users
Example: The Investigatory Powers Act (UK) allows bulk data collection from VPNs without warrants.
2. Intelligence Alliances
The Five Eyes network (US, UK, Canada, Australia, NZ) shares VPN data through:
- US Cloud Act: Compels U.S.-based providers to surrender data regardless of server location
- Mutual Legal Assistance Treaties (MLATs): Bypass jurisdictional barriers
3. Covert Partnerships
VPN providers often face undisclosed national security letters (NSLs) that:
- Prohibit disclosing government data requests
- Require modifying infrastructure for surveillance
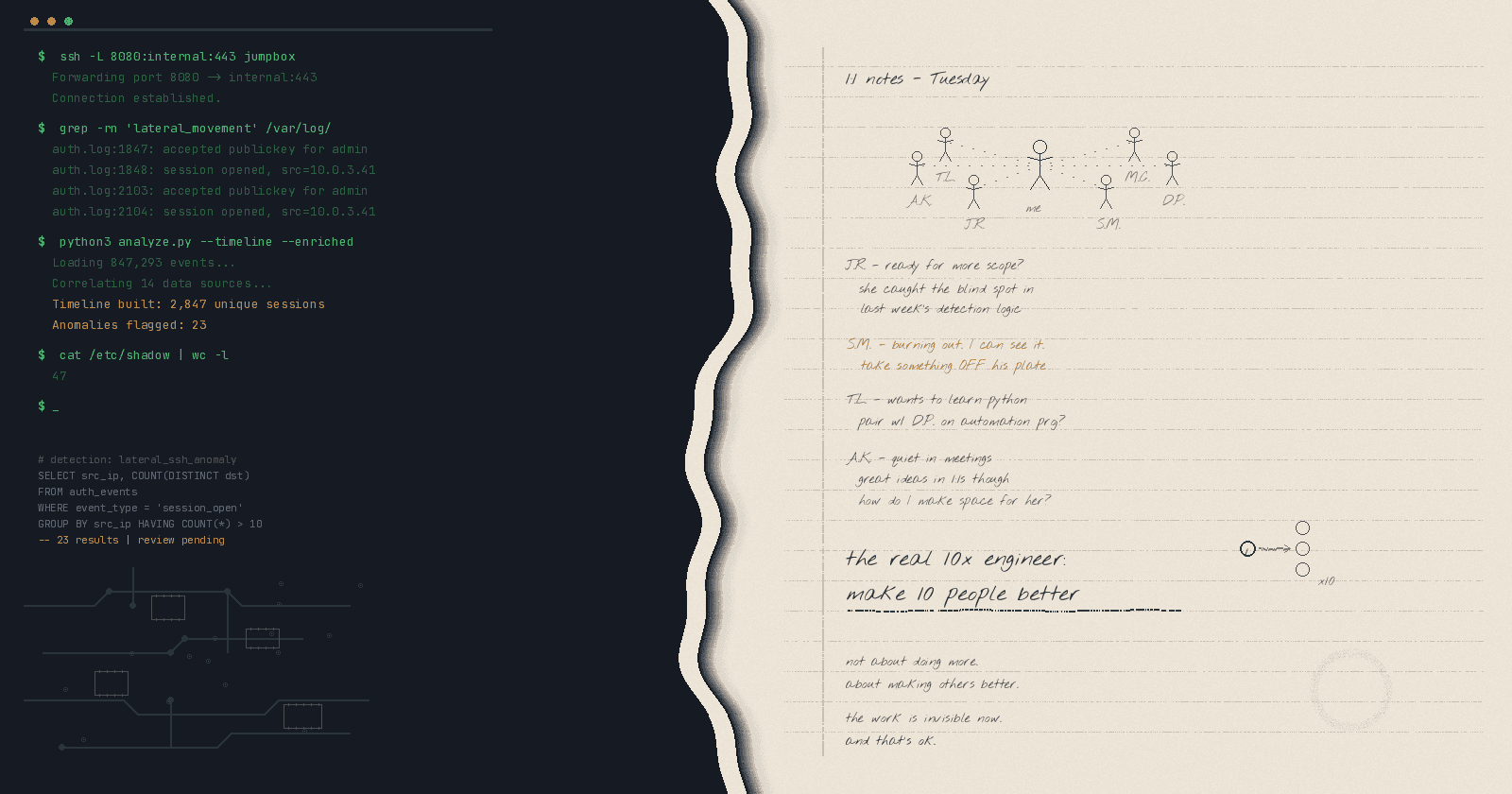
Why Private VPNs Like Tailscale Solve These Risks
Architecture: Centralized vs. Decentralized

Reference: Tailscale — A traditional hub-and-spoke VPN (centralized)
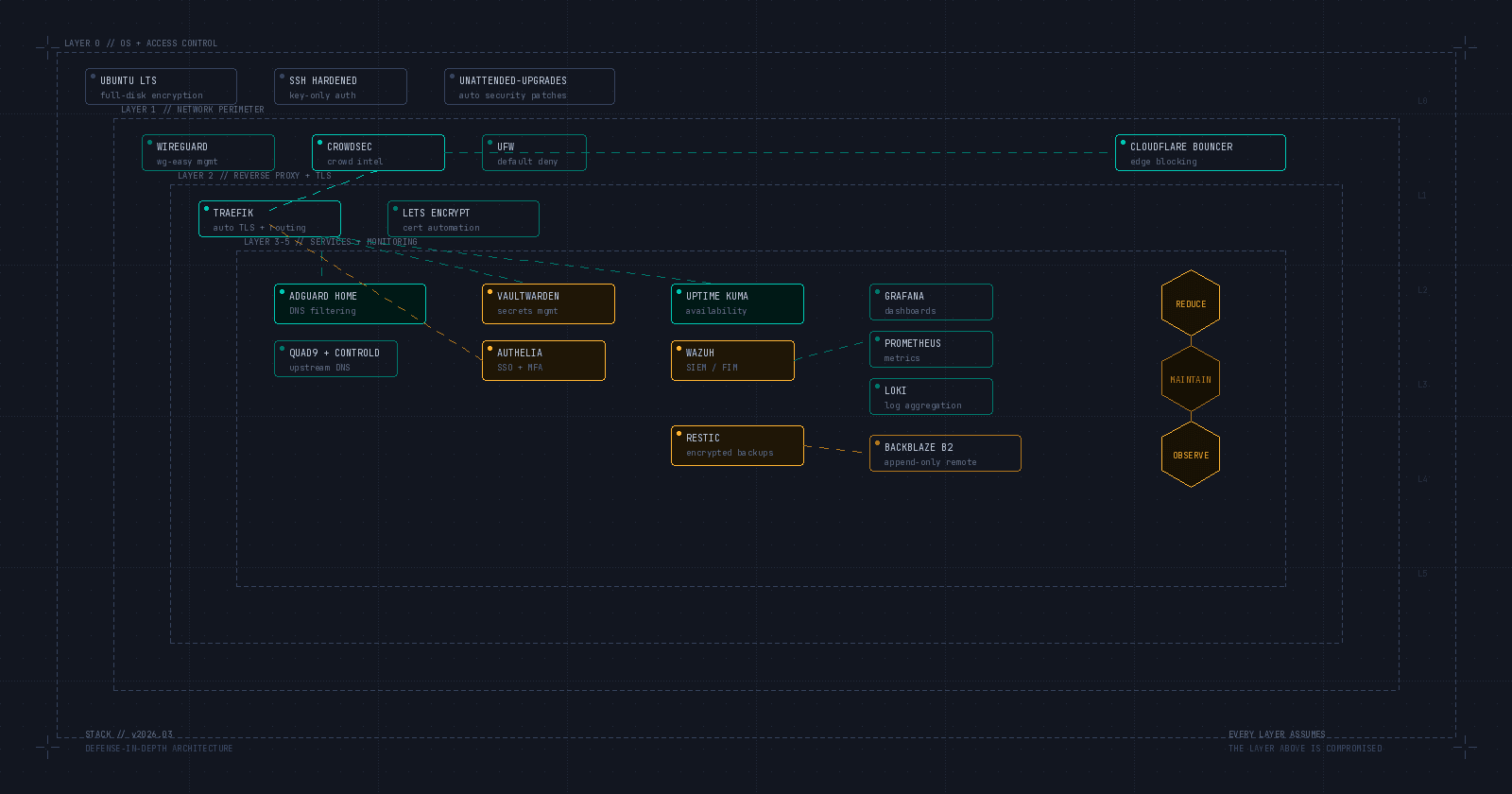
Tailscale uses a peer-to-peer mesh network where:
- Devices connect directly (no central server)
- WireGuard encrypts traffic end-to-end
- Keys stay on user devices (not even Tailscale can access them)

Reference: Tailscale — A Tailscale point-to-point mesh network (decentralized)
5 Key Anti-Surveillance Features
- Zero Trust Authentication: Devices authenticate via SSO/MFA, not shared credentials
- DERP Relay Avoidance: Prefers direct connections; uses relays only as backups
- No Central Logs: Tailscale’s control plane manages connections but can’t decrypt traffic
- Self-Hostable Control Servers: Tools like Headscale let you host the coordination server
- NAT Traversal: Works behind restrictive firewalls without port forwarding
Limitations of Private VPN Solutions
Technical Barriers
- Headscale Configuration: Requires Docker/CLI expertise vs. commercial apps
- No Geo-Spoofing: Tailscale doesn’t mask your location for streaming
Corporate Risks
- Relay Latency: DERP servers add 30–100ms latency in poor NAT setups
- No Layer 7 Filtering: Can’t block specific websites/apps
Legal Gray Areas
- Home Server Subpoenas: ISPs may log your self-hosted VPN’s IP
- Cross-Border Data Laws: GDPR still applies to EU user traffic
Recommendations for Secure Networking
1. For Individuals:
- Use Tailscale’s free tier for device-to-device access
- Enable Shields Up mode to block unsolicited inbound connections
2. For Enterprises:
- Deploy Headscale on air-gapped infrastructure
- Combine Tailscale with Cloudflare Tunnel for public-facing apps
3. For High-Risk Users:
- Route traffic through Tor before hitting Tailscale nodes
- Use mTLS to authenticate device fingerprints
The Future Is Decentralized
Commercial VPNs’ centralized architecture makes them inevitable targets for government coercion — whether through subpoenas, server seizures, or insider threats. Cases like Safe-Inet and IPVanish prove no-log policies are meaningless when faced with lawful intercepts.
Private solutions like Tailscale eliminate single points of failure through:
- End-to-end encryption immune to provider compromise
- Self-hostable control planes (via Headscale)
- Open-source transparency
While not perfect, they represent a philosophical shift: privacy isn’t a service to purchase, but a system to architect.